Twitter CEO Jack Dorsey Explains Why He Banned Trump
Charlie Kirk Staff
01/14/2021

Latest News
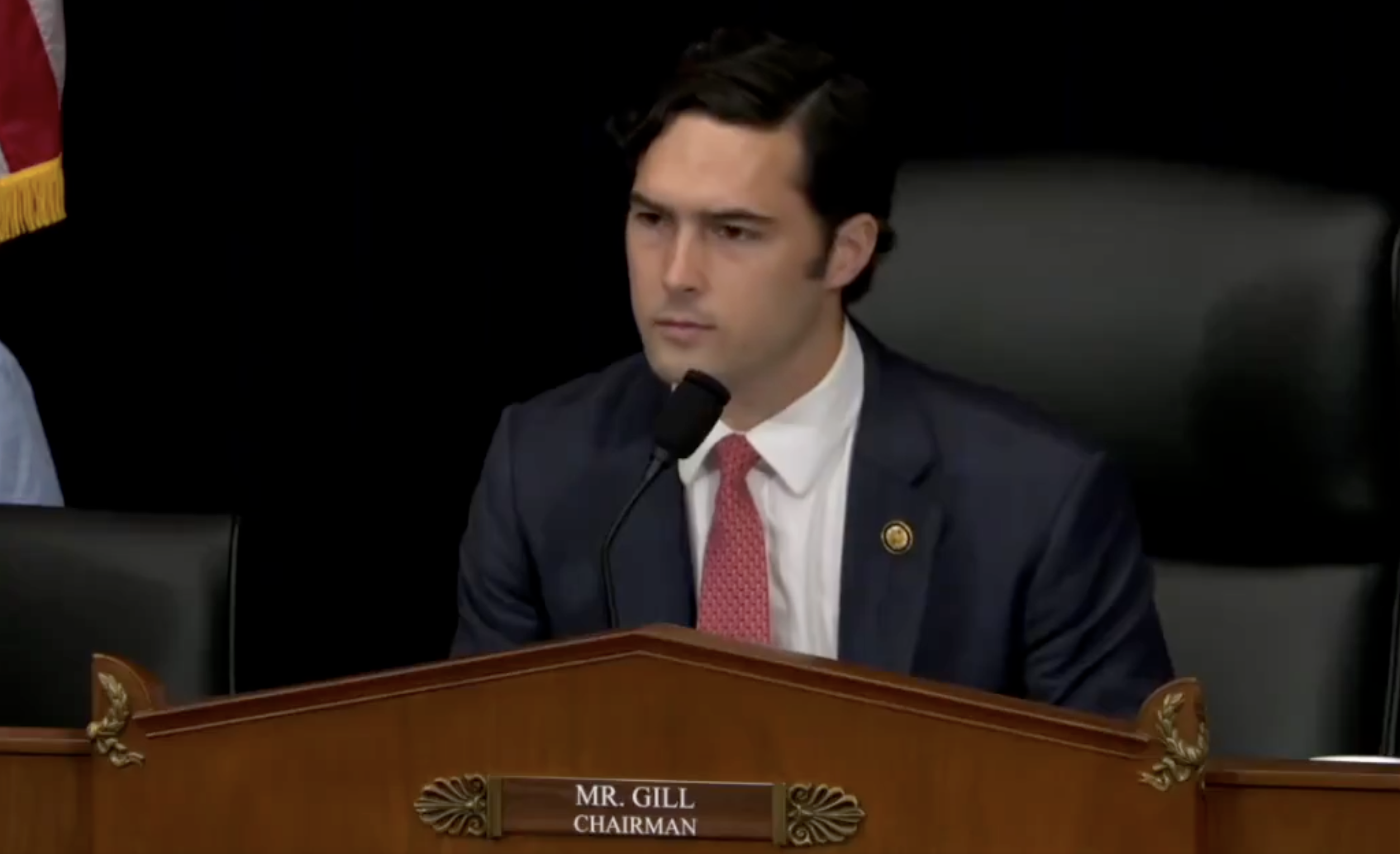
Rep. Brandon Gill Goes NUCLEAR On Somali Fraud During Heated Task Force Hearing

SPLC Helped Pay For KKK Cross Burnings, Robes And Hoods, Hate Group Recruitment: Indictment

University Of California Professors Demand Return Of Standardized Testing As Academic Performance Plummets

 Member
Member









